Decrypting column-level encrypted data depends on the encryption method used and the encryption key management system. Generally, to decrypt data that has been column-level encrypted, you need access to the decryption key and use the appropriate decryption algorithm.
Here, follow some general steps to decrypting column-level encrypted data:
- Obtain the decryption key: You need access to the decryption key used to encrypt the column. The key can be stored in a key management system, a hardware security module (HSM), or a secure database.
- Identify the encryption algorithm: Determine the encryption algorithm used to encrypt the data. Common encryption algorithms include AES (Advanced Encryption Standard), RSA (Rivest-Shamir-Adleman), and others.
Write a query to find the encrypted key and algorithm: –
select * from sys.symmetric_keys
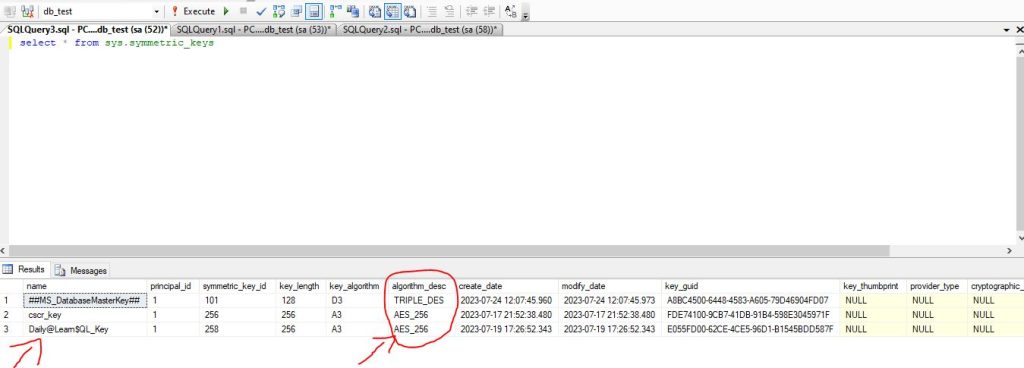
Here, you can find the name of the encrypted, the algorithm name, created date, and the modified date according to the image.
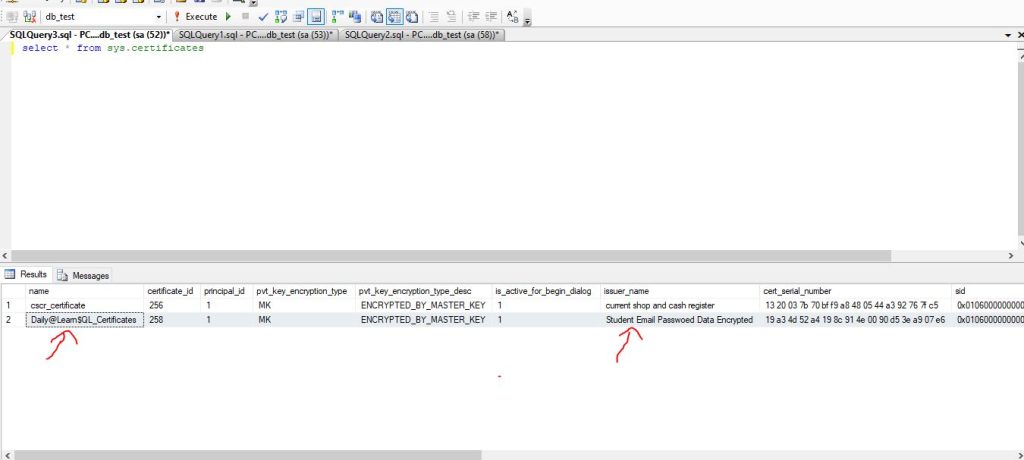
Write a SQL query to find the encrypted server certificate: –
select * from sys.certificates
- Use the decryption algorithm: Once you find the decryption key and decryption certificate, and know the encryption algorithm, then open the symmetric key with an encrypted password and use the appropriate decryption algorithm to decrypt the encrypted data.
- Apply decryption to the data: For each encrypted value in the column, apply the decryption algorithm using the decryption key to obtain the original plaintext value.
OPEN SYMMECTRIC KEY Daily@Learn$QL_Key DECRYPTION BY CERTIFICATE Daily@Learn$QL_Certificates; GO SELECT CONVERT(VARCHAR(128), DECRYPTBYKEY([EmailPass])) FROM tbl_Student
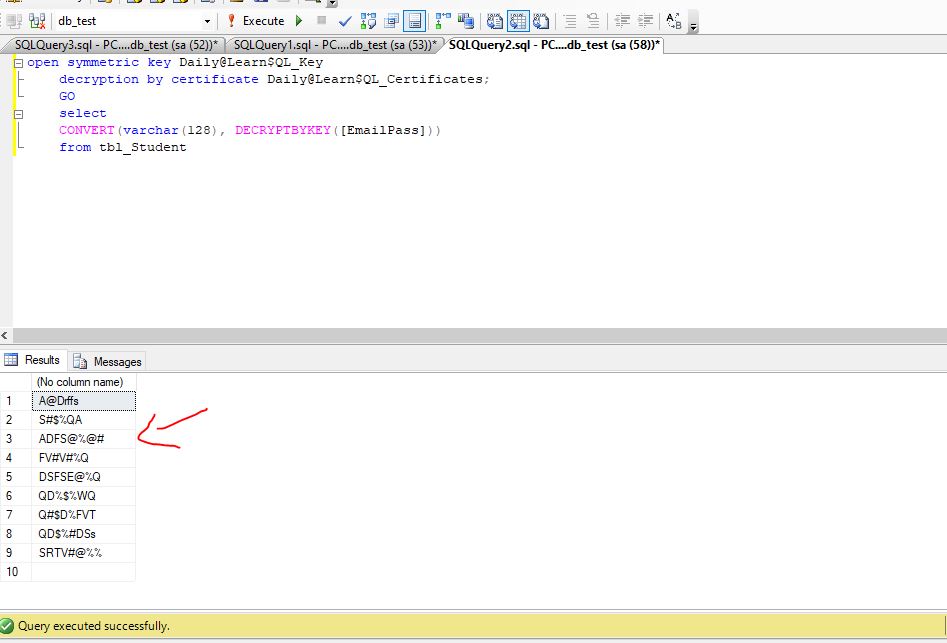
Once you apply this decryption query to your database, you will find your original decrypt data on the SQL server. Make sure that you have a master key and certificate key on the specific database, otherwise, you need to create a master key and certificate key on that database. On the other hand, once you find the certificate and master key then you don’t need to create it again, instead of this you need to regenerate the Master key and certificate again.
If you are working with a specific database or encryption system, consult the documentation provided by the vendor for detailed instructions on decrypting column-level encrypted data within that system.